Android
DROID DOES
Welcome to the droidymcdroidface-iest, Lemmyest (Lemmiest), test, bestest, phoniest, pluckiest, snarkiest, and spiciest Android community on Lemmy (Do not respond)! Here you can participate in amazing discussions and events relating to all things Android.
The rules for posting and commenting, besides the rules defined here for lemmy.world, are as follows:
Rules
1. All posts must be relevant to Android devices/operating system.
2. Posts cannot be illegal or NSFW material.
3. No spam, self promotion, or upvote farming. Sources engaging in these behavior will be added to the Blacklist.
4. Non-whitelisted bots will be banned.
5. Engage respectfully: Harassment, flamebaiting, bad faith engagement, or agenda posting will result in your posts being removed. Excessive violations will result in temporary or permanent ban, depending on severity.
6. Memes are not allowed to be posts, but are allowed in the comments.
7. Posts from clickbait sources are heavily discouraged. Please de-clickbait titles if it needs to be submitted.
8. Submission statements of any length composed of your own thoughts inside the post text field are mandatory for any microblog posts, and are optional but recommended for article/image/video posts.
Community Resources:
We are Android girls*,
In our Lemmy.world.
The back is plastic,
It's fantastic.
*Well, not just girls: people of all gender identities are welcomed here.
Our Partner Communities:
view the rest of the comments
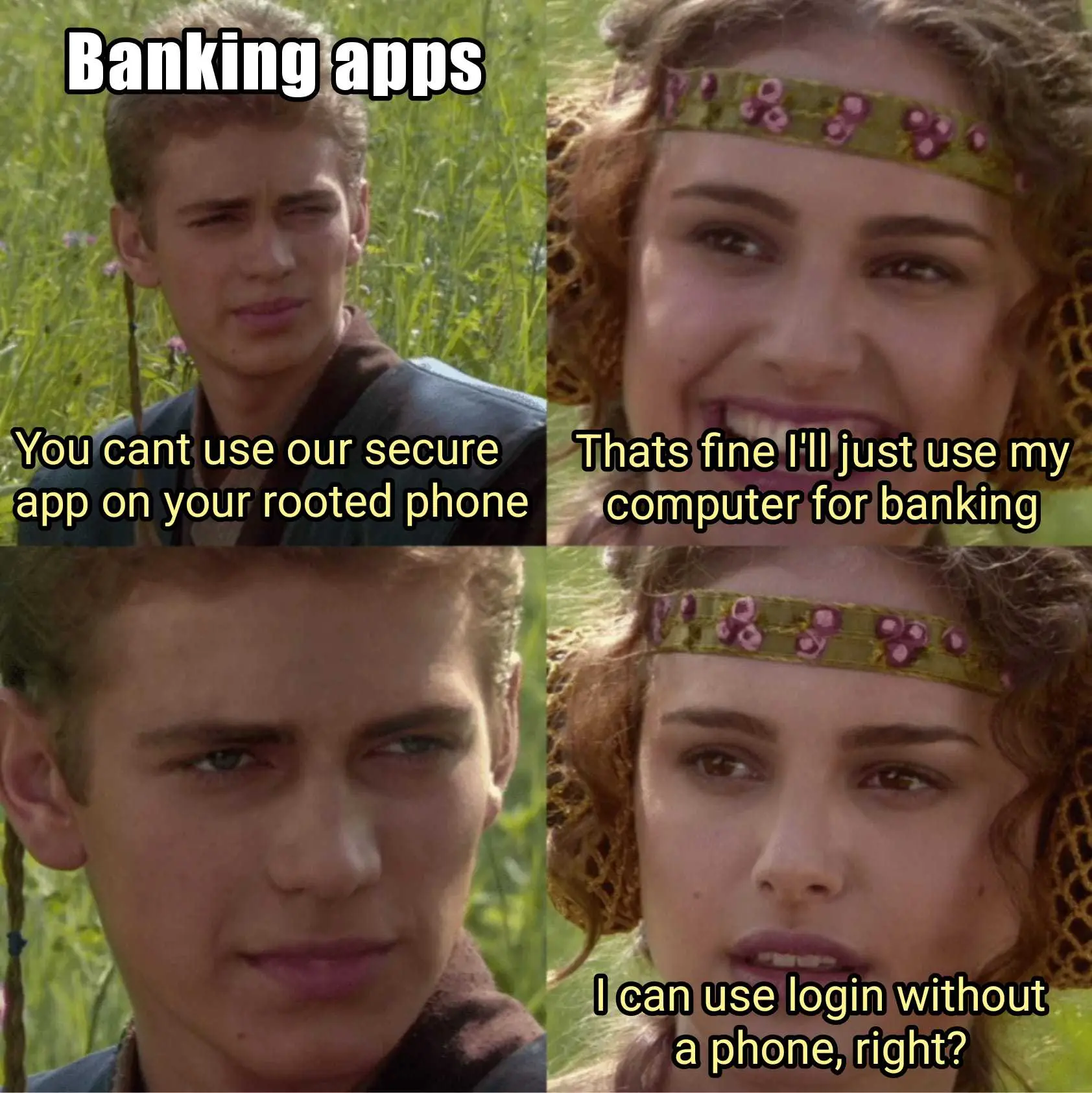
What are the security issues? Rooted just means the potential to give trusted apps root access. Of course, if you give an app root access that you trust but is then abusing that trust and being malicious, yes it's a security issue. But if you don't do that, the simple fact of having a rooted phone should have no security change in any way. (Ok, except for potential bugs in Magisk/su or whatever)
The whole issue revolves around the fact Google is presuming a device is compromised or being used for illicit shit simply because root access is possible. If they put in effort to detect/prevent the actual problems they're concerned about, this wouldn't be as big a deal. This broad punishment for simply having root access is lazy and ridiculous.
It's like if Windows apps just stopped working if they detected a local admin account. It's patently absurd to assume the ability to access anything means the device is inherently "unsafe".
But the previous commenter talked about security issues, you're only talking about usability issues.
https://www.reddit.com/r/GrapheneOS/comments/13264di/comment/ji54e19/?utm_source=share&utm_medium=mweb3x&utm_name=mweb3xcss&utm_term=1&utm_content=share_button
I'm pretty sure whoever wrote that was talking out their ass. The fuck is "UI layer" on Android, or rather, what does it have to do with it xD
The actual Magisk prompt that ask you if you want to give root to such app. This UI layer.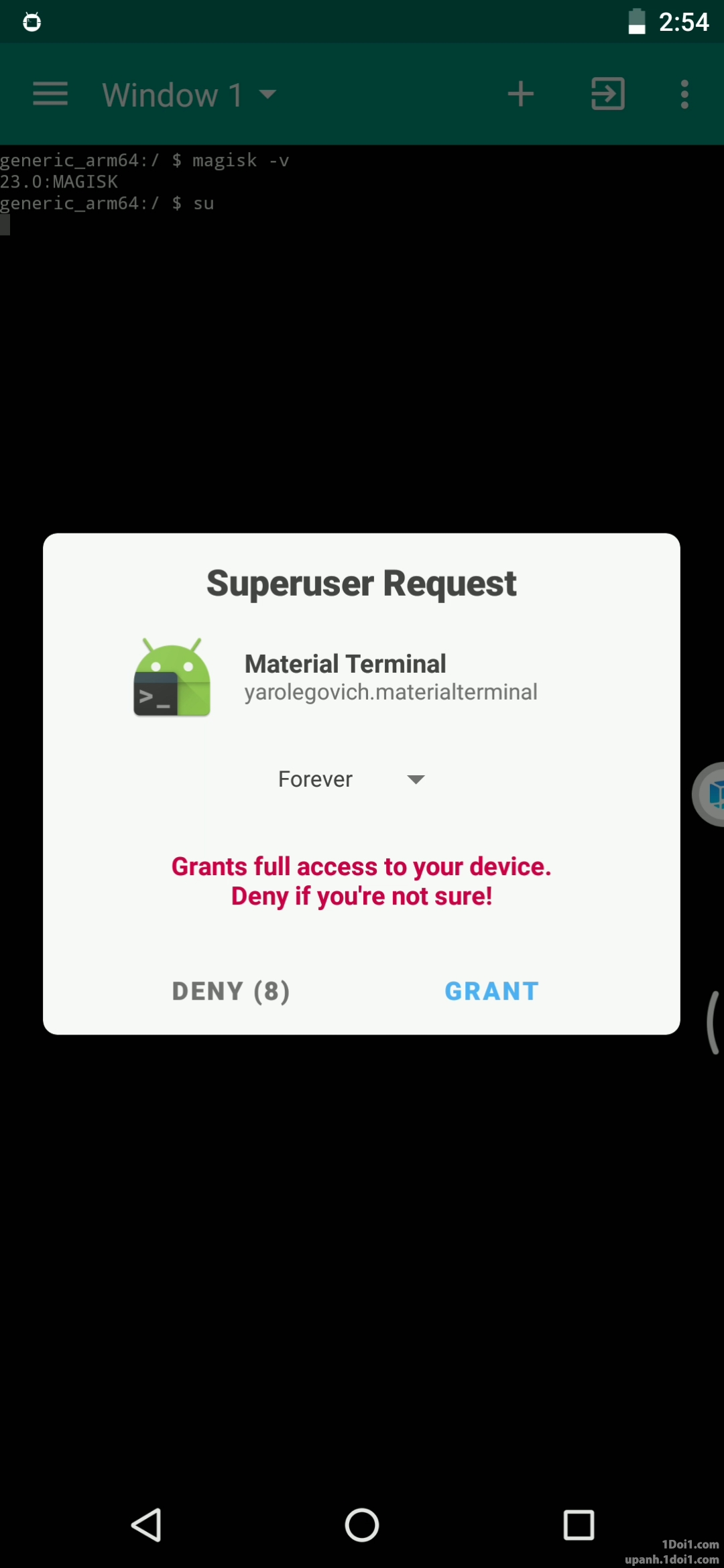
Although, i suppose it could be countered by explicitly refusing all requests or enabling a biometric confirmation
But granting root is not done by "the UI layer", "the UI layer" is not running with root. There is no such thing as "the UI layer" as a separate entity, an app can have a UI layer as part of its architecture, but the UI is not running on its own. Just because Magisk shows you a UI for you to grant/deny a root request, that doesn't make it insecure. Nothing is able to interact with this prompt except the Android kernel/libraries itself and Magisk.
Only if you added an application as accessibility tool (or give it root) can it interact with anything within the UI. An app with a UI is generally not much different than an app on the command line.
It still create an attack vector, as it allows a potential extra method to get access to it, in addition of potential hardware exploits that i shared to gain root. Yes, you can minimize the risks correctly, but the user is the only real barrier against it, not the software anymore. The less potential way to exploit your phone, the better it is. You shouldn't rely on thinking that such feature is fully attack-proof.