Lemmy
Everything about Lemmy; bugs, gripes, praises, and advocacy.
For discussion about the lemmy.ml instance, go to !meta@lemmy.ml.
This is why password managers are so heavily pushed. Imagine if you used the same password for Lemmy that you used for your email? Both are now compromised. A unique password for all accounts is the bare minimum you must do.
Although it is worth noting that the recent Lemmy hack didn't come from a password compromise, but from session token harvesting, which a password change would not really protect against.
Lol this is not how the hack worked. JWT cookies are encrypted. They don’t contain your password at all. There was no way to reverse engineer from your cookie to your password.
I literally just got one last week. It's so nice! I guess I was hesitant because centralized passwords always put me off, but it's not hard to setup 2FA on all your important stuff.
Sorry, but that's literally every online service. For example if you buy a new virtual server it takes like 5 minutes till a Chinese IP starts to try root passwords.
If someone actually wanted to harm Lemmy they'd just DDOS the biggest instances for a month (which would be easy, it's mostly single servers after all) or attack it with so much spam and large images that storage would break.
We need moderation tools
Here's hoping Sync and Boost lead the way
Here's hoping Sync and Boost lead the way
Or better yet, let's hope Free Software apps lead the way and ditch the proprietary ones.
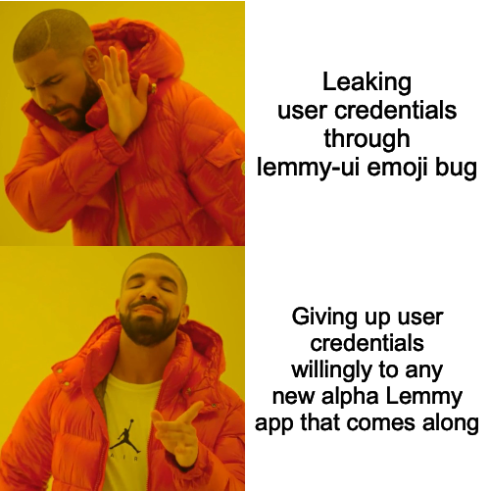
Using open source apps, especially with more than one contributor, is currently the best option to be safe from this kind of attack.
Edit: I'm not saying that FOSS is 100% secure because it's FOSS. I'm just saying it's the best option we currently have.
It helps, but it's still not a silver bullet. For example, a Lemmy app could contain no malicious code in its open source repository, but malicious code could still be added to a binary release in an app store.
Voyager (formerly wefwef) is a self-hostable web app, so it doesn't have this problem. Of course this only means you can inspect the code you're running. You still have to able to understand the code to be sure it's not doing anything malicious.
That's why F-Droid is the safest Android app repository. If I'm not mistaken, every app they offer is rebuilt from the public source code by the repo package maintainer.
The safest option would be for Lemmy to implement OAuth and apps that aren't in some "official front end for xyz website mode" to authorize via OAuth with the backend instead of via credentials.
Most if not all Mastodon/Pleroma apps already use OAuth by default. I'm surprised that Lemmy hasn't implemented it yet. I wonder if KBin does already?
No, because open source apps need to have enough eyes on them to spot malicious code. And highly complex ones need proper audits and even that might not be enough to catch every fancy vulnerability.
I doubt a malicious actor would open source their app tho
That's fair, but sometimes a malicious actor will attempt to covertly contribute code that introduces a security vulnerability.
My lemmy account is made with a throwaway email and with a randomly generated password just in case it ever gets leaked
I didn't even attach an email to mine.
Thanks for the heads up. My password is %f22N$CBTNgW, can you let me know if it was leaked?
pls also check hunter2
What is it? I only see ******. I think Lemmy is hiding personal info now.
Pretty funny but if you enter you actual password it will hide it. My pass is ************, which should show up as asterisks for you.
Try it out. Pretty cool security feature honestly.
hunter2
We need your full name, date of birth and zip code to check
I am using the Liftoff app. It looks pretty safe but I don't really know.
It's open source and pretty popular (for a Lemmy app at least) so it should be pretty safe
Are there any known apps that should be avoided? I’m using Mlem and Memmy.
Not yet, this post is just a warning that it might happen
Not sure about the other apps, but Memmy keeps your password stored in the app. But generally speaking I don’t think Gavin is a malicious person. He spent 3 weeks with beta tests before he was even comfortable pushing it to Apple App Store and the code is reviewed by Apple before being included to watch for malicious scripting. I am not saying people don’t get malicious scripts passed through Apple, but from what I have seen of Gavin’s work, he doesn’t seem the type that would do that.
Me reading this post on an alpha app on testflight: chuckles I’m in danger.
Kidding aside, I used a dedicated email (and password) for my account and don’t plan to post any personal info on here.
1password is probably the most valuable subscription I pay for.
If anyone's looking for a free and open source option, Bitwarden is also great.
Indeed, this is a real weak spot with Lemmy's security. I honestly think we need to place more emphasis on implementing OAuth2, when I have the time I'll have to take a look at that again to see if I'm able to.
Thanks for this!!
I feel like it raises somewhat the general issue of how much we're willing to live with complete mysterious anonymity from all of the developers and admins in the fediverse. I'm not saying that every admin or developer should have their real identity revealed and linked here. But there's a tension or issue here in how much it's normal and accepted and how much the fediverse in general wants to grow and attract users that are accustomed to trusting large companies that provide a different kind of base level trustworthiness than makes sense "out here".
If not links to real life identities (however trustworthy that can be in the limit), at least some connection to a broader online presence such that it becomes more likely the actor has something to lose in acting in bad faith (the lemmy core devs being a good example).
I don't have a solution ... but it seems to be a growing pain as this whole thing kind of grows from "hacker project" to "mainstream social media".
The solution has been the same for the last 20 years: Use a password manager, do not reuse passwords. That's it, you're done.
Even if the Lemmy instance admin steals your password (which would be easy!) they can't do anything with it.
What about the app Memmy for iPhone ?
Preface: I have no opinion. Have not installed, and will not install because I don't need it.
If you have to ask, it's probably worth investigating further.
The first thing I would do is search around for any mention of the app name and variants on the word "password".
Never install anything that you don't trust, and dissociate from your "real" email/identity for those that you aren't sure about. Whoever owns the software potentially owns your credentials.