this post was submitted on 23 Apr 2024
1054 points (97.1% liked)
Memes
45730 readers
1152 users here now
Rules:
- Be civil and nice.
- Try not to excessively repost, as a rule of thumb, wait at least 2 months to do it if you have to.
founded 5 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
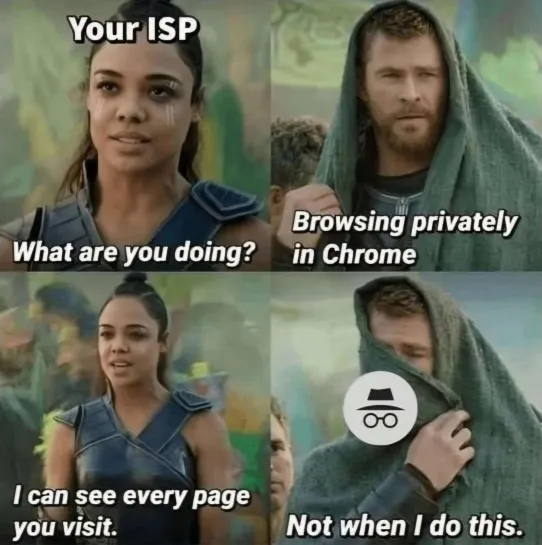
Use Mullvad, iVPN or Proton and they really won't see what you're doing
with Mullvad and iVPN, be sure to use the quantum encryption. And to help obscure your traffic with proton, be sure to use a proxy that has around 50% to 60% usage. That way anyone who tries to use a quantum computer to break the encryption on a proton VPN proxy is going to see everyone else's traffic using that proxy as well as you. There would be a lot of shit to go through even if they use a quantum computer.
So your threat model assumes an actor with a quantum computer capable of breaking RSA, but not a regular computer capable of filtering by IP address?
filtering by IP address how?
the IP address of your modem? Well your ISP will easily be able to tell whether or not you're using a VPN. And I guess at that level if someone used a quantum computer on your modem's connection from the modem to the proxy, then yeah, they'd probably be able to evesdrop as long as they have access to the lines from your house to the hub of your local ISP and the VPN you're using doesn't have quantum-safe encryption.
If you're in a position where you'd need to worry about a corporation or government using a quantum computer to get into your shit you've got bigger problems.
From what I understand, it requires a fuck-ton of electricity to run a quantum PC and they'd need to use even more electricity on top of that to keep it cool in a refrigerated room at sub-zero temperatures.
But that's only what all the tech-companies making them are currently saying. There's probably more advanced stuff that they're keeping secret. We'll never know until another whistleblower sacrifices their entire life to tell the world about it.
A VPN encrypts traffic between your device and the VPN server, and any packet on that path includes your IP address. So anyone attempting to decrypt your VPN traffic can trivially distinguish your packets from other users of the VPN server.
A VPN is only a single end point just like your ISP meaning you are only shifting the problem to your VPN provider who admittedly is more trustworthy than your ISP but you are still putting an immense amount of trust into a single point of failure.
If you truly want to hide from your ISP or really anyone, your only options are to use TOR or I2P where your traffic is encrypted and tumbled through multiple servers.
Absolutely no one is using quantum computers to brute force encryption, stop the fear mongering.