this post was submitted on 11 Nov 2023
-84 points (11.1% liked)
Privacy
31872 readers
542 users here now
A place to discuss privacy and freedom in the digital world.
Privacy has become a very important issue in modern society, with companies and governments constantly abusing their power, more and more people are waking up to the importance of digital privacy.
In this community everyone is welcome to post links and discuss topics related to privacy.
Some Rules
- Posting a link to a website containing tracking isn't great, if contents of the website are behind a paywall maybe copy them into the post
- Don't promote proprietary software
- Try to keep things on topic
- If you have a question, please try searching for previous discussions, maybe it has already been answered
- Reposts are fine, but should have at least a couple of weeks in between so that the post can reach a new audience
- Be nice :)
Related communities
Chat rooms
-
[Matrix/Element]Dead
much thanks to @gary_host_laptop for the logo design :)
founded 5 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
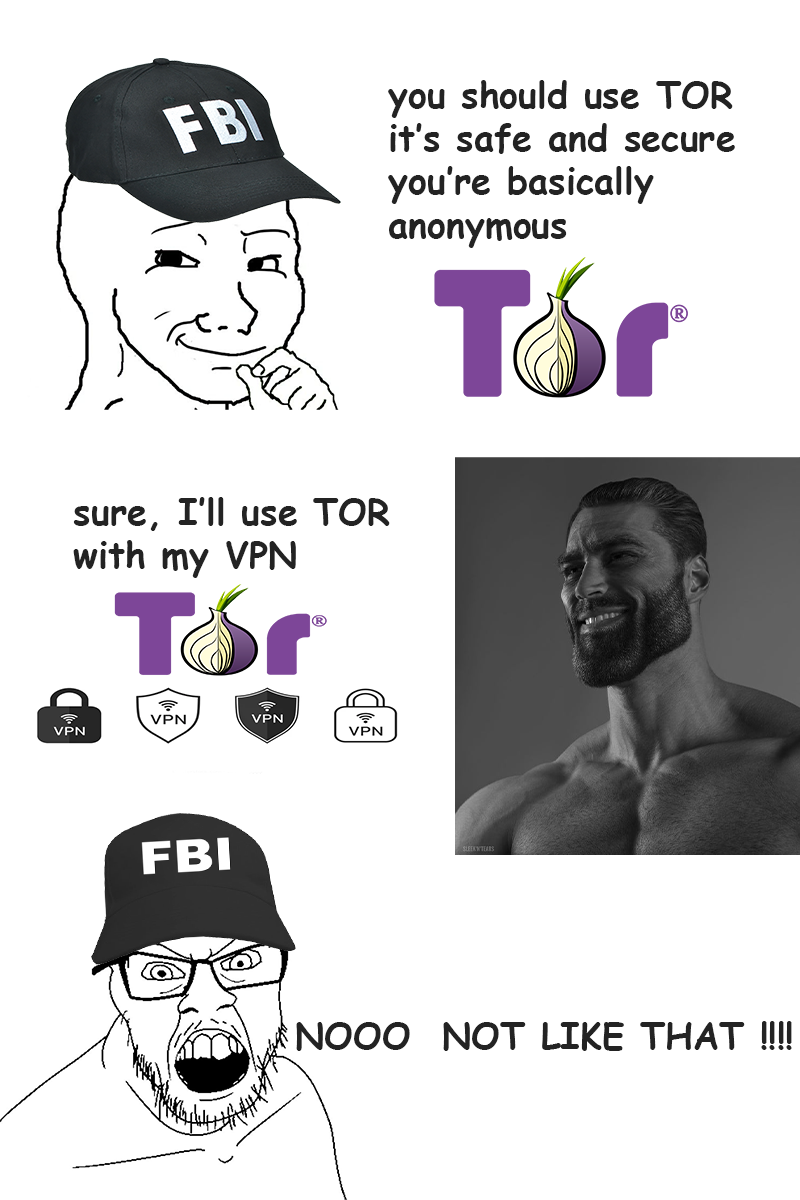
Well all this normie learned (me) was not much. What’s the safer play then?
You don’t gotta link me to computer science journals, I can’t read any of that cryptographic hieroglyphic RSA 6969bit new world mumbo jumbo.
Just half assed memes about secop.
Depends on what you wanna do with TOR. If you wanna be anonymous in your regular internet browsing and torrents, go with a good quality paid for VPN with no logs, like mullvad or proton. You don't need TOR at all. You're not worth the hassle.
If you're trying to commit chill crimes like ordering drugs online, then you should probably look up the DNM bible. Just TOR and maybe a bridge is enough probably, if people where you live in don't use TOR. LEO can't see your traffic but if you're the only one using TOR in your neighborhood, it's pretty easy to pin you.
If you're a journalist and you're about to piss off a powerful government, you probably need a bridge and TOR and a laptop with no hard drive. You will probably need some self hosted machines to obfuscate your traffic which you will need to recycle really often. You shouldn't use a phone. You also need a lot of money and a lot of help, specially in countries that are against the country you're pissing off. Opsec becomes a full time job, depending on how many friends you have.
If you're trying to run a drug empire or distribute CSAM, getting caught is merely a question of when no matter what you use, because even politically divergent countries and organizations will unite to put you in jail, even if they're normally on the crime side of things. Nobody likes CSAM distributors and drug empires usually don't make a lot of friends and make way too much money to keep the ones they do.
Based ass response. I honestly had no clue about that neighborhood point. I’m honestly shocked and thankful you explained that.
A dude got caught making bomb threats at Harvard because he was the only one in his university that connected to TOR and they knew from the entry node it had to be from that area. They checked the logs and only one PC had directly connected to the TOR network from that area at that time. The guy wanted more time to study.
He could've easily avoided that by simply connecting through public coffee shop wifi instead of being a dumbass...
so tails os on a flash drive with olny floss programs and the duck mp3 player from the dankpods video
And a separate flash with your password database, PGP keyring and an encrypted files vault. If you need to go or to destroy/hide evidence, a flash drive is much easier, specially when the task force going after you is more worried about hard drives and laptops and usually gloss over flash drives at least initially.
I feel like anyone who has to do anything that "deep cover" is probably doing some hyper aggressive prevention techniques as well like creating a botnet and their own "private" Tor which they recycle machines frequently, or using stolen/compromised VPS and only connecting to it via proxy chains, or something similarly complex.