this post was submitted on 12 Sep 2023
1195 points (97.8% liked)
linuxmemes
21263 readers
506 users here now
Hint: :q!
Sister communities:
- LemmyMemes: Memes
- LemmyShitpost: Anything and everything goes.
- RISA: Star Trek memes and shitposts
Community rules (click to expand)
1. Follow the site-wide rules
- Instance-wide TOS: https://legal.lemmy.world/tos/
- Lemmy code of conduct: https://join-lemmy.org/docs/code_of_conduct.html
2. Be civil
- Understand the difference between a joke and an insult.
- Do not harrass or attack members of the community for any reason.
- Leave remarks of "peasantry" to the PCMR community. If you dislike an OS/service/application, attack the thing you dislike, not the individuals who use it. Some people may not have a choice.
- Bigotry will not be tolerated.
- These rules are somewhat loosened when the subject is a public figure. Still, do not attack their person or incite harrassment.
3. Post Linux-related content
- Including Unix and BSD.
- Non-Linux content is acceptable as long as it makes a reference to Linux. For example, the poorly made mockery of
sudoin Windows. - No porn. Even if you watch it on a Linux machine.
4. No recent reposts
- Everybody uses Arch btw, can't quit Vim, and wants to interject for a moment. You can stop now.
Please report posts and comments that break these rules!
founded 1 year ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
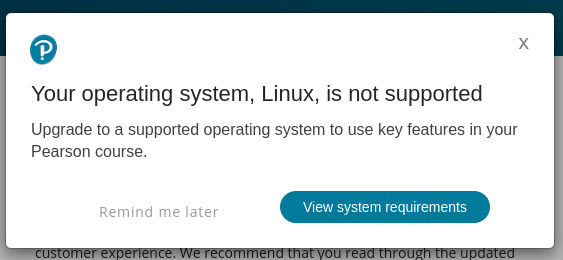
Just change your user agent. Fuckers have no business knowing.
Won't work if you're using their test software. That shit is more invasive than anticheat
Then vm it is
They can detect that too - at least, they can detect the common software. You might be able to do it with a custom QEMU setup but good luck guaranteeing that for your exam.
I used to be a reseller of this highly specialized navigation software. The licensing was handled via hardware fingerprinting of the harddrive. I'm not 100% sure on how it worked, but it grabbed some raw data off of the boot device, and from that generated a fingerprint. This fingerprint was then sent to the guys who made the software, and they would then send us a license key and a hefty bill. The license key only worked with syatems running off of that particular harddrive. If a customer had a harddrive failure, we had to send them the actual harddrive for them to verify, so they would issue a free key to whichever replacement drive was used.
I did a lot of experimenting with that software. It was linux based and very tweakable, but the licensing part of it was a bit of a mystery. I managed to crack it through some surprisingly simple out-of-the-box thinking, but one limitation I could never figure out how to circumvent was its refusal to generate a fingerprint from virtual drives.
For starters, it only worked with drives registering as /dev/hdX or /dev/sdX. Anything outside of that and it wouldn't generate a fingerprint.
This was especially frustrating when a well-paying customer offered a nice bonus if we could install it on a macbook for him. After a few days of tweaking I managed to install and run it, only to discover that fingerprinting the drive couldn't be done due to the device node being/dev/nvmeSomething. And after avfew more days of hacking I managed to fake that too, and they outright refused to issue a license due to them not wanting to support our unofficial hacks.
Where was I going with this? Oh, right, vmware.. i never managed to get it to run in vmware. We had this other well paying customer who wanted the ability to alt-tab between the software and Windows. Unfortunately, any fingerprinting done from within vmware, regardless how I set up the storage, resulted in a fingerprint file with no data.
Fun fact: the software ui was written in raw xlib. I got to know the owner and lead dev fairly well, and he hinted that the codebase was a complete mess to the point where something as simple as an input dialog for a config option I recommended was A LOT of work.
I would love to know how that's possible.
The easy way involves looking at the devices and drivers you have installed. Things like a VirtualBox display or a SPICE guest driver are dead giveaways. next, they might look at your processor and see if it has as many cores as it should, but that's more involved.
Holy shit why is it even getting anywhere near that nosy? I didn't know it was anything like that. And I even worked for them for a little while.
Because it also serves as an anti-cheat...in the most literal sense. It is trying to make sure students can't cheat by having other things open like answer pages or Google.
Oh, duh. That seems a little obvious in retrospect. But damn, they go pretty harsh then.
The qualifications industry is heavily reputation based. If they get a reputation for letting cheaters slide, their reputation tanks among employers and therefore no one will want that qualification.
And these qualifications are expensive as hell too.
Unfortunately they probably have detection methods for that, so have fun trying to work around that.
Meaning it doesn't run in wine?
Yep. This is by design - it's trying to detect container software that stops it from seeing what else is running.
But wine is no container software.
Technically true, but programs loaded via WINE can be made to act somewhat containerised, and can provide incomplete information as to what else is running. Maybe containerisation is the wrong word though, maybe 'sandbox' instead?
Good luck detecting Linux native programs from WINE-loaded Windows executables.
Yes, and at least there's no more ms activex bullshit to fail either (looks like S. Korea finally got rid of it 3 years ago too).